Problem
On a Nessus PCI Scan SMB Signing Disabled was flagged up as a vulnerability.
Nessus Output
Description
Signing is not required on the remote SMB server. An unauthenticated, remote attacker can exploit this to conduct man-in-the-middle attacks against the SMB server.
Solution
Enforce message signing in the host's configuration. On Windows, this is found in the policy setting 'Microsoft network server: Digitally sign communications (always)'. On Samba, the setting is called 'server signing'. See the 'see also' links for further details.
Resolution
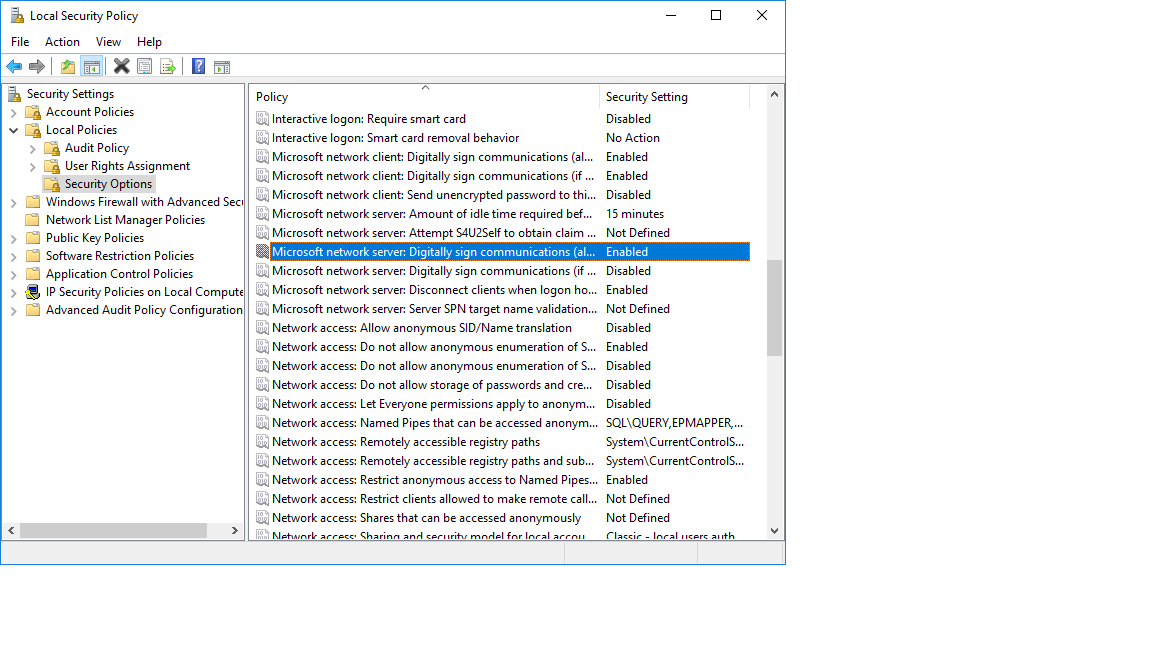
On the affected server. Open Administrative Tools -> Local Security Policy -> Local Policies > Security Options
Enable the following Policies:
Microsoft network client: Digitally sign communications (always) Microsoft network server: Digitally sign communications (always)
You must be logged in to post a comment.